Mobile Hacking Labs: Strings Challenge
Welcome to the Strings Challenge! Reverse engineer the Android app and retrieve the hidden flag using dynamic analysis techniques.
Objective
Reverse engineer the Android app com.mobilehackinglab.challenge and retrieve the hidden flag in the format MHL{...} using dynamic analysis techniques (Frida, Fridump). The app is intentionally vulnerable for educational purposes.
Tools Used
- Frida
- Fridump
- ADB
- APKTool
- Emulator (Android x86_64, API 28)
Initial Steps and Setup
-
APK Analysis:
- Decompiled APK using JADX-GUI.
- Found obfuscated Java code with minimal static analysis value.
- Identified exported activities:
MainActivityandActivity2.
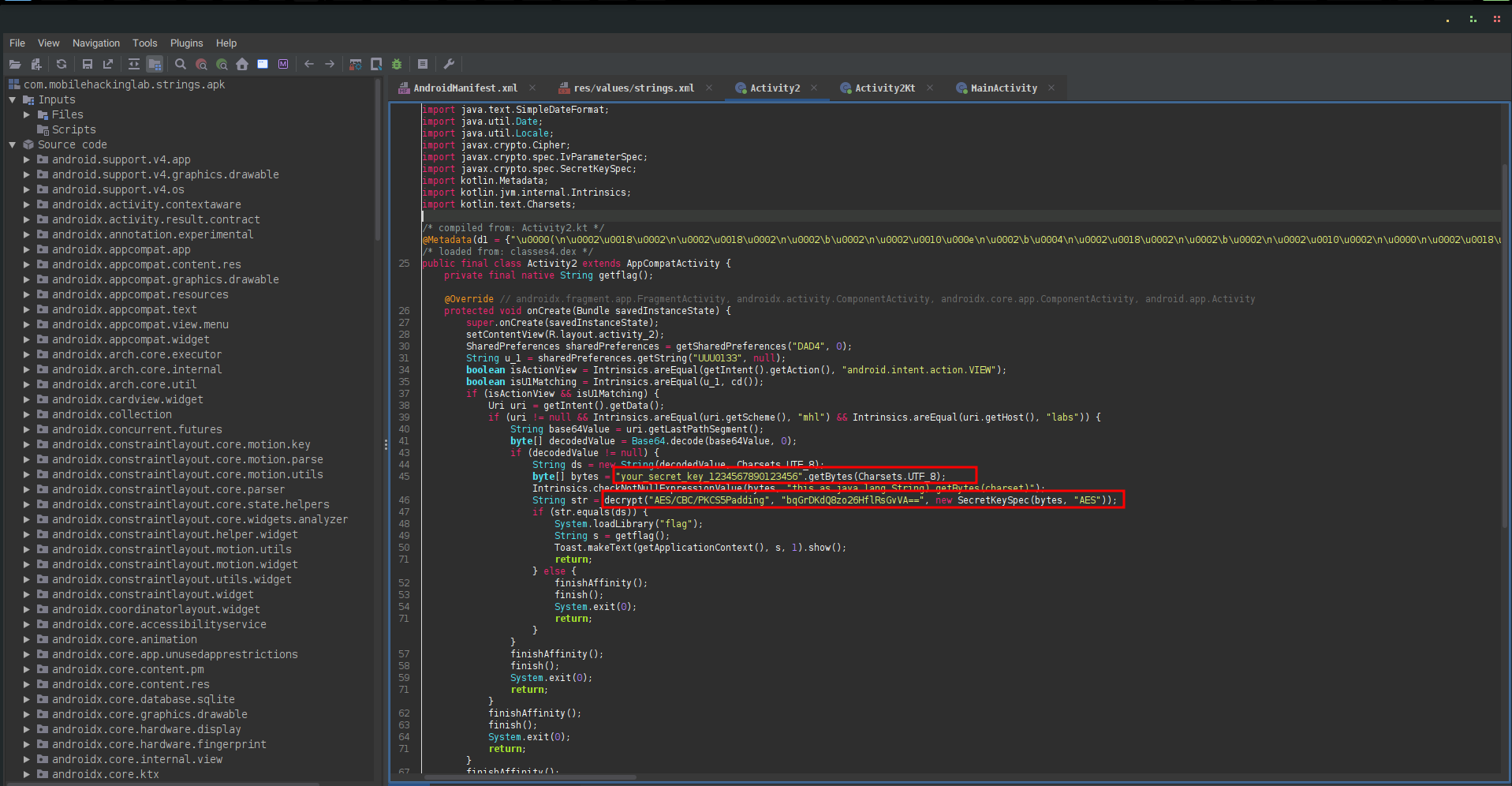
- Hardcoded Strings:
- Secret key:
"your_secret_key_1234567890123456" - Encrypted message:
"bqGrDKdQ8zo26HflRsGvVA==" - IV in
Activity2Kt.fixedIV
- Secret key:
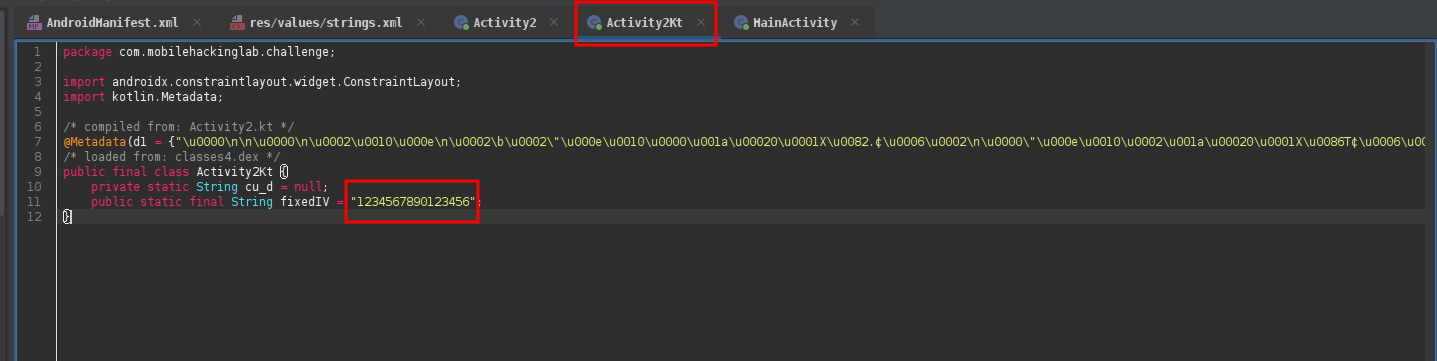
IV string is
1234567890123456 -
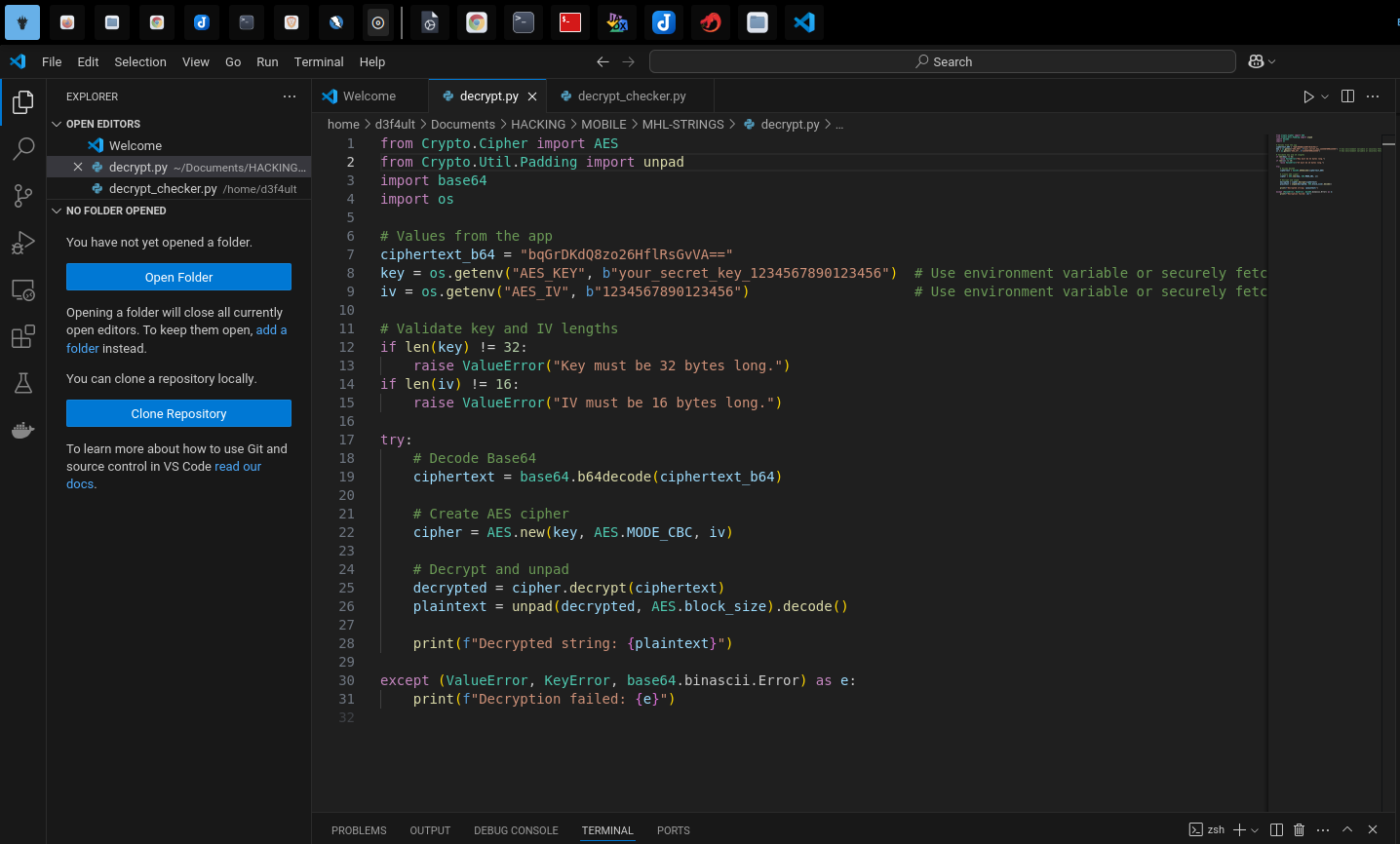
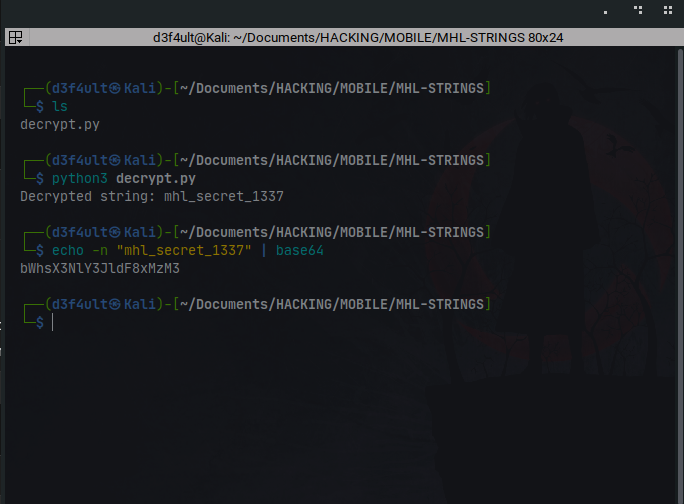
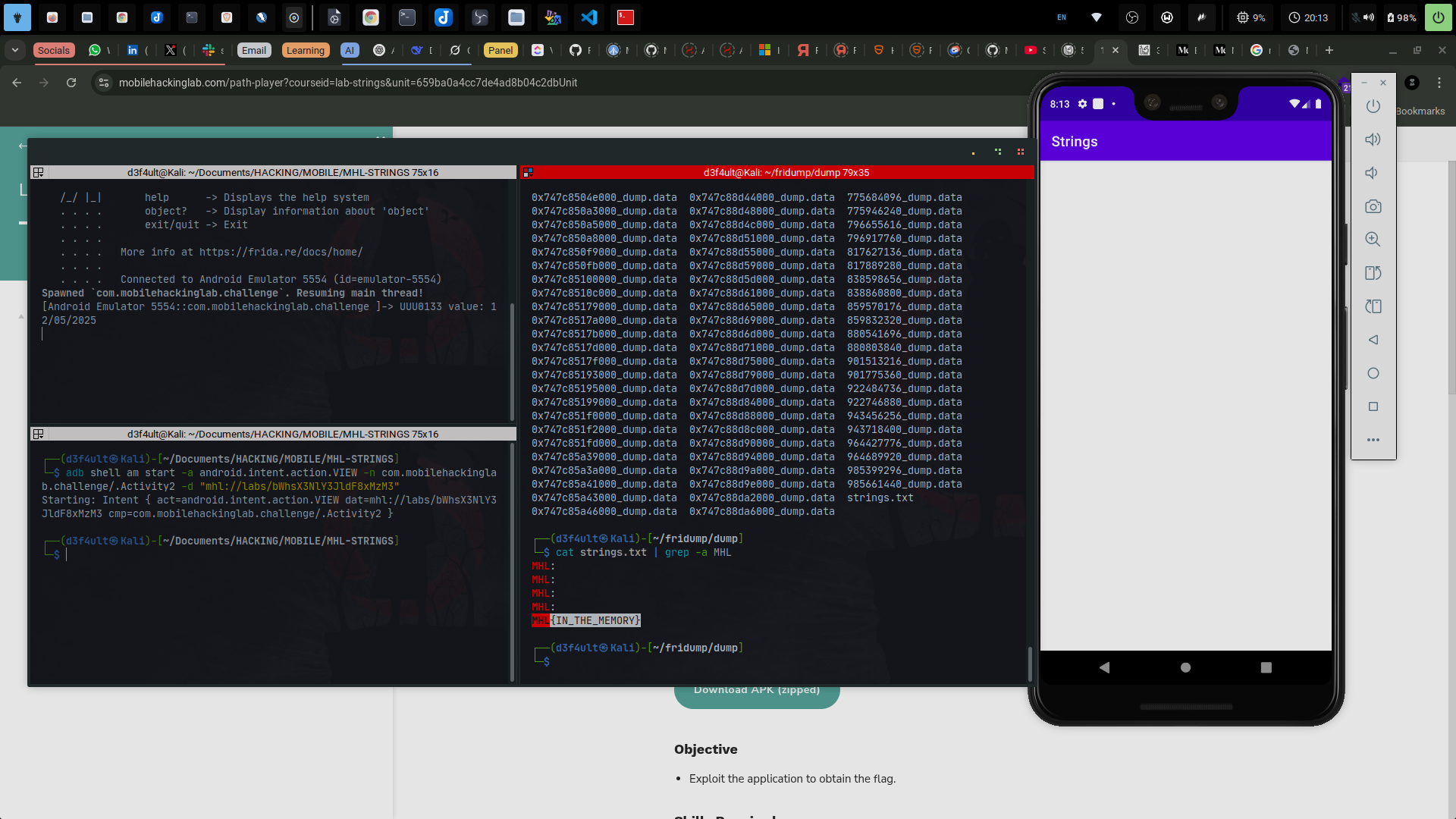
Cracking the Code:
- Wrote a Python script to decrypt the key:
- Got the key:
mhl_secret_1337 - Encoded the secret with base64, as the code checks for a deeplink:
mhl://labs/bqGrDKdQ8zo26HflRsGvVA==(deeplink)
-
Frida Hooking:
- Bypassed
SharedPreferencescheck and triggered the intent using a Frida script:
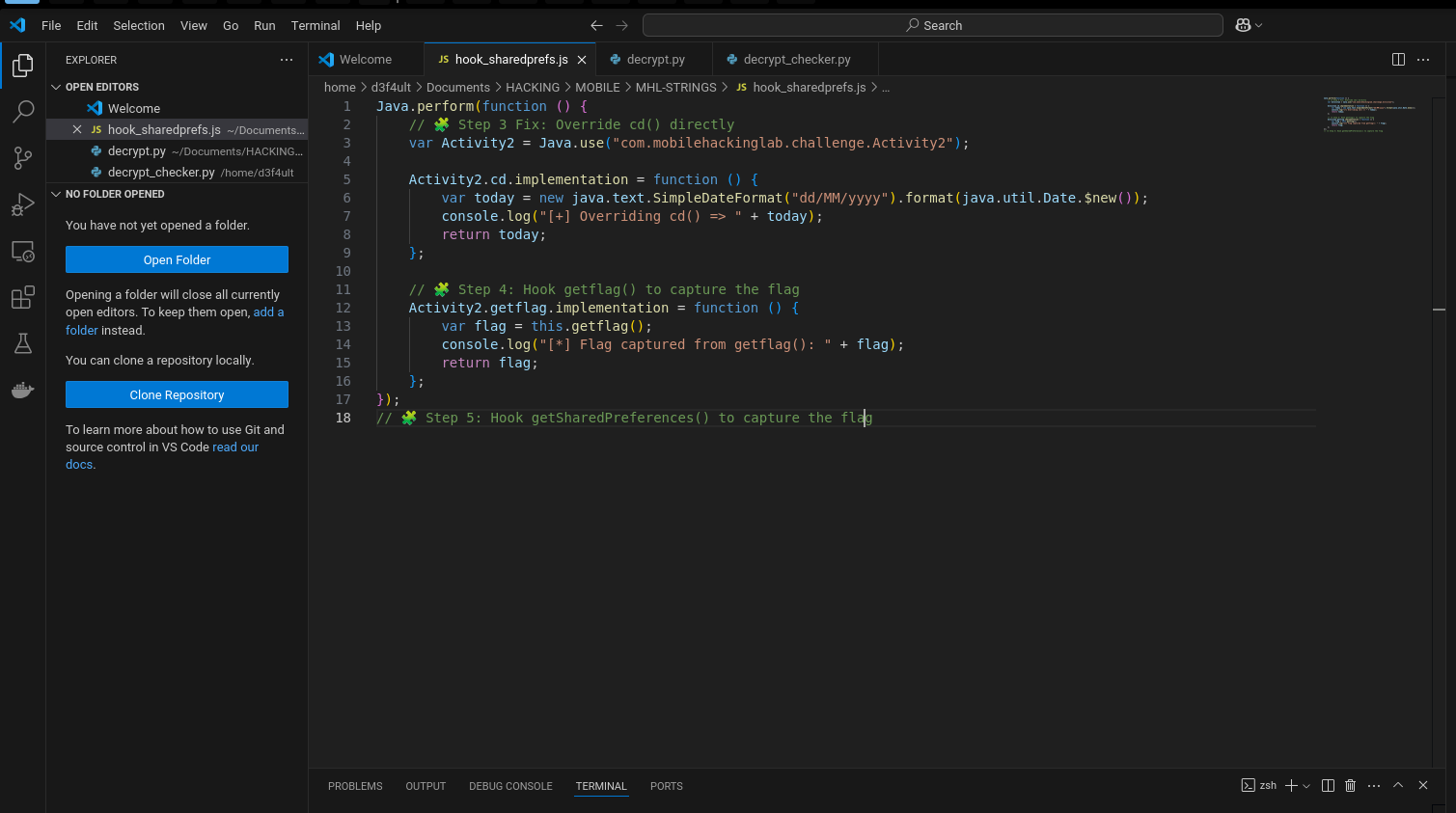
Ran this command:
adb shell am start -a android.intent.action.VIEW -n com.mobilehackinglab.challenge/.Activity2 -d "mhl://labs/bWhsX3NlY3JldF8xMzM3"Triggered the exported activity, got success, but no flag:
- Bypassed
Troubleshooting & Final Solution
-
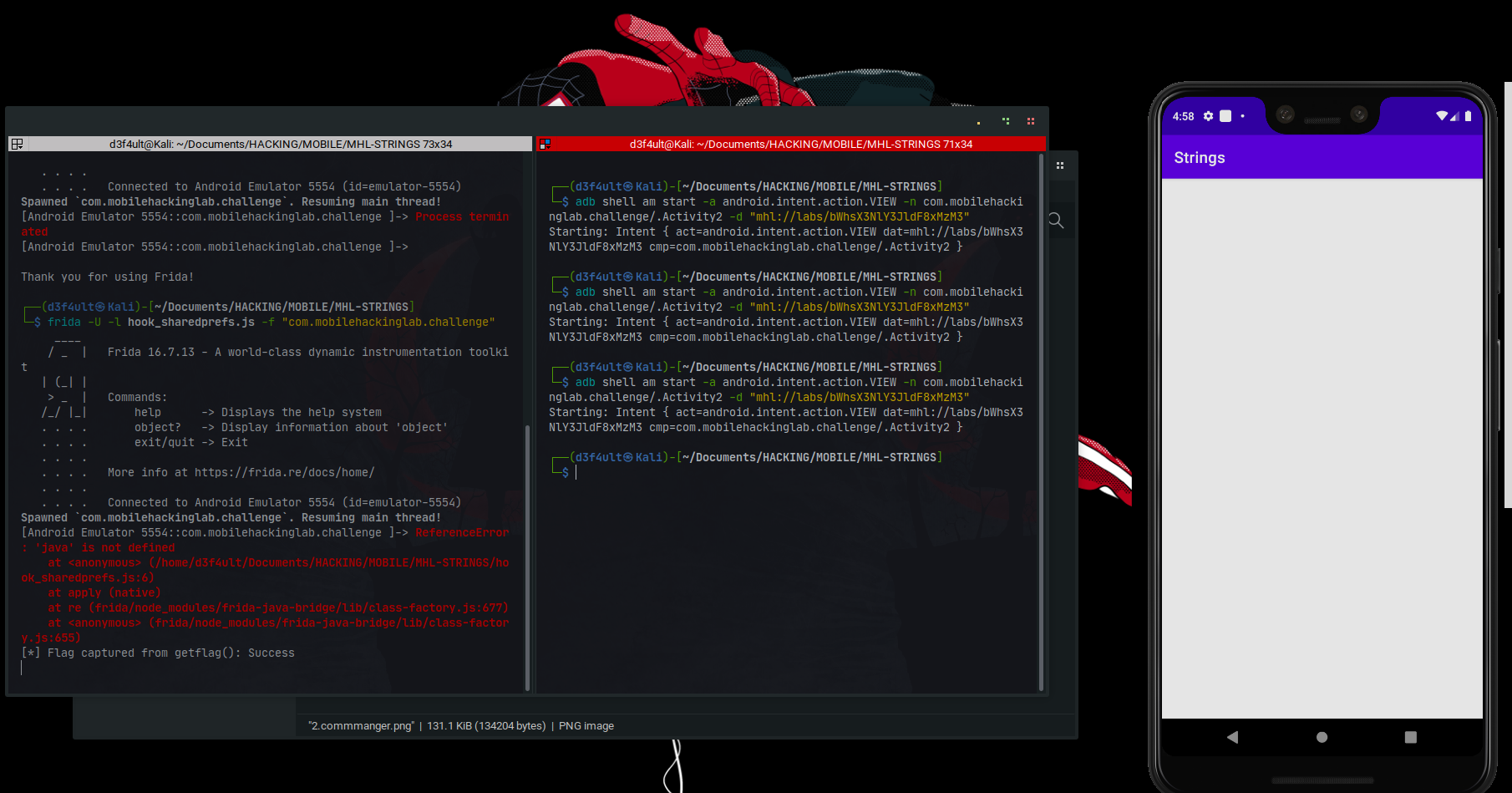
Errors, Errors, Errors!
- Tried to hook a Frida script to dump memory, but got many errors:
- Probably because I was using an emulator.
- Also tried Ghidra for reverse engineering, but was unsuccessful.
-
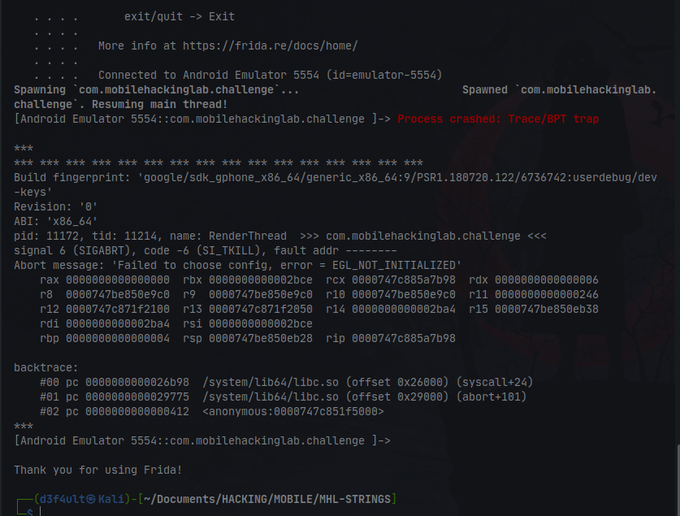
After Research:
- Used Fridump to dump memory, and it worked!
python3 fridump.py -U -s Strings
🎉 Flag Retrieved!
Successfully extracted the hidden flag using Fridump memory dumping technique.
